Elves at Work
Wishing that all your days are happy … [1 min. read]
Wishing that all your days are happy … [1 min. read]
In an ongoing effort to elude this year’s frustrating shipping delays, more consumers are turning to the web for what they may see as easy answers to the holiday hassle. Vasu Jakkal VP Microsoft Security said that with “headlines about supply chain issues, worker shortages and costs rising … it’s no surprise that … at least sixty-three percent of holiday shopping will be done online.”
While most of the Bryley team works from the Clinton office, I’m physically distanced, writing at home. And as the days have grown to months in this work-from-home-if-you-can-work-from-home world, our perspectives change as our settling-in has changed us. So here’s a bit of remote work advice, for the times they are still a-changin’.
Alongside links to Amazon, Home Depot, Staples, etc. Google’s sponsored shopping sections also show unfamiliar stores with lower prices than those of the well-known retailers. But are these really good deals?
Here are some ways to see if an inexpensive site is really going to get you what you want. None of these are absolute rules; the more information you have to make your decision about trusting an unknown website with your account or other personal information, the better sense you can get whether it’s worth making the bargain.
Phishing emails are getting more complex all the time. As the stakes rise, cyber criminals are employing increasingly subtle techniques and messaging. Gone are the days when you simply had to turn down preposterous offers from royalty who had miraculously decided to become your unlikely benefactor.
The phishing email of today is designed to look as legitimate as possible. It will try to distract you from clues that give away its true intent by creating a sense of urgency. Typically they front as legitimate emails from familiar sources, sometimes even appearing to come from within your own organization.
Fortunately, once you know what to look for, these emails will be as easy to spot as those starting “I am a prince from [insert random country name here], and I wish to bathe you in riches…”
“All they had to do was come up with a way to charge ten bucks a month and now no one steals music,” I overheard a college student say. He was talking about how Apple transformed from selling software (mp3s via iTunes) to renting access to songs, aka Software as a Service (SaaS). Apple Music now has the most paid music subscribers in the US and based on this success, “announced new subscription offerings for magazines, TV shows and video games”. 1
Per Forbes, 84% of new software is being delivered as SaaS. 2 This selling model built Netflix memberships (20 million renters at the height of its DVD service compared to over 150 million SaaS subscribers today 3 ), Dollar Shave Club razors, Stitch Fix and Amazon’s Subscribe and Save. Subscriptions moved Adobe’s market cap more than 87% since 2012 to $108 billion. 4
 “Support for Windows 7 is Coming to an End. … January 14, 2020 …” nagged a Windows 7 screen last week.
“Support for Windows 7 is Coming to an End. … January 14, 2020 …” nagged a Windows 7 screen last week.
Like any other piece of technology, Operating System software gets obsolete. The obsolescence comes in the form of vulnerabilities to hackers, who get rich knowing how to look for and exploit these weaknesses in the code, compromising the contents of your computer and network.
Obsolescence also comes from more powerful hardware at a relative lower cost that enables the OS to do more with less code. Greater efficiencies in hardware and software mean some businesses will accomplish the same work as other businesses in less time.
And among the more compelling features of Windows 10 is that developers’s apps can scale to work across platforms, so desktops, laptops, phones and tablets function with the same software without the formerly prohibitive development costs of coding from scratch for each device. The result is more robust and cost-efficient software that, for example, can control processes remotely.
But this does not mean you are without legitimate reasons for maintaining Windows 7 software that works for you. The law requires you to have access to the data created with that software: “judges … have potent sanctions options available … when [businesses treat electronic data] preservation … with ignorance, indifference”
https://www.jdsupra.com/legalnews/bad-behavior-in-ediscovery-is-still-30811/
So it is important to maintain your organization’s data created in legacy software. You or an IT partner will need to develop strategies for addressing your organization’s dependence on legacy software. This is sometimes a technical process requiring the involvement of third-party specialists. For instance, some legacy software was built to utilize 16-bit chip architecture. Windows 10’s 64-bit version does not support 16-bit programming. Still Microsoft has made a way to get you the benefits of 64-bit Windows 10, and still allow you to run 16-bit and 32-bit software through virtual machine environments. These virtual machines will probably get you enough access to meet compliance issues, but interface changes may render the legacy apps limited in function. Overcoming these types of challenges might not be appropriate to handle on your own.
If your organization has multiple Windows 7 licenses, the upgrade path can be costly, and not just for the multiple new OS product keys. There may be costs related to replacing your legacy software beyond the cost of the software itself. It is important to consider implementation costs, including possible downtime and employee training. Be sure to work with your IT department or partner to ensure that these considerations are included in your upgrade plan.
An IT partner like Bryley can help come up with a plan to meet your specific upgrade needs, so your business functions productively through the end of Windows 7 and the use of legacy apps, to arrive at solutions that will work for the coming years. Bryley can be reached at 978.562.6077 Option 2. With 32 years of experience, Bryley’s professionals have a broad knowledge of business software and can guide you with your business’s Windows 10 transition.
By default, when you close Google Chrome, the browser window closes, but the application itself continues to run in the background. There are a few reasons for this.
First and foremost, this makes it faster to open a new browser window. Since Chrome is already running in the background, there is less that has to take place behind the scenes before your new browser window appears. This makes the browser feel quick, even on slower machines.
Running in the background also allows any Chrome extensions you might have installed to continue to operate. These are applications that run within Chrome and either enhance the browser’s existing features, or add new ones. Extensions range from those that change Chrome’s background colors to those that add support for third party applications.
This behavior, however, might not always be desirable.
If you are running an older or less powerful computer, you might find that forcing Google Chrome to stop running in the background could noticeably improve the overall performance of your computer.
Similarly, if you are using a laptop, having Google Chrome running in the background could negatively impact your battery life. By forcing Chrome to close completely, you might find you can stretch your battery life just a little further.
If you fall into one of these two categories, or would simply prefer to avoid having Chrome run in the background, you can follow the instructions below to disable this behavior.
1. Select “Settings” in the Chrome Menu
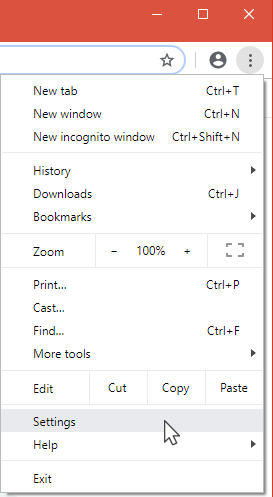
2. Click on “Advanced” at the bottom of the settings page that appears.
3. Under the “System” heading, find the box next to “Continue running background apps when Google Chrome is closed.”
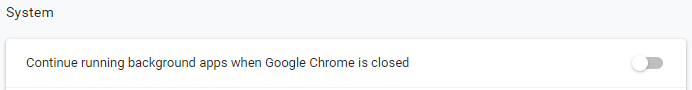
By default, the toggle button next to that text will be set to the right with a blue background. To prevent Chrome from running in the background, simply click the button so that the toggle is to the left, with a gray background (see screenshot above).
If, in the future, you decide you would like to allow Chrome to run in the background once again, simply repeat the steps above and move the toggle back to the right.
The 2015 Arkansas murder case that depended on smart-home devices, made the news again as the judge in the civil case upheld his ruling that James Bates is financially liable for the death of Victor Collins. The case against the accused was built on, among other forensics, records from Amazon whose Echo device was installed by the scene of Collins’ death, as well as evidence from a so-called smart meter. The smart meter reported inordinate usage of water around the time of death, which led the police to argue that a bloody patio was hosed down.
A sense of belonging, a sense of community and for businesspeople, a touchpoint for customer service and the ability to market to specific demographics are among social media’s benefits. And like every technology, social media – by which I mean websites that offer sharing tools that allow people to interact (e.g. Instagram, Twitter, SnapChat, Facebook, YouTube) – have their drawbacks.
Call our business managed IT services department directly at (978) 547-7221 or simply fill out this form and we will get in touch with you to set up a getting-to-know-you introductory phone call.
200 Union Street Clinton, MA 01510
© Copyright 2024 BRYLEY. All Rights Reserved. Website in partnership with Tech Pro Marketing. | Privacy Policy
