Lawrence Strauss
Google has by far the most comprehensive data on the web. Its business is virtually completely dependent on people using its search engine. This means it has an enormous interest in keeping searchers satisfied, that neither an upstart nor Microsoft overtakes it (as it did to AltaVista). And, given its wealth, it purchases the best talent to constantly improve its search function, continually fulfilling the promise of artificial intelligence while acting less like a malleable machine1.
And if you want sales on the Internet, given the market share we surfers have granted it, there’s no avoiding Google.
So how can you get your site highly ranked by Google? The answer: SEO (Search Engine Optimization) developed in the wake of the explosive growth of the web.
Twenty years ago there was no “Optimization”; you were trying to appeal to the fledgling Yahoo’s employees, who could manage to look at and review every site. But when machines supplanted people because of web-page volume, the software could be fooled with myriad techniques, including the popular and persistent keywords:meta tags. (Please see Search Engine madness by Lawrence Strauss in the April 2016 edition of Bryley Information and Tips.)
Because its business is built almost exclusively on search results, Google got much better at understanding site owners and seeing through their desire to be ranked first, and their techniques to get there. So what’s come about is a return to the only really timeless technique, memorably expressed by Phil Frost; the Golden Rule of SEO is create the web page you would want to find if you were searching.
But first a diversion into much less poetic territory; like life itself, Google isn’t fair.
Big business breaks the rules all the time and Google rewards it with the best rankings. Take for example the Microsoft-founded travel site Expedia: Expedia was penalized (i.e. knocked down on some search results) by Google for violating its rules about manufacturing in-bound links. (In-bound links, or links on other sites pointing to Expedia, are meant to be understood by Google’s PageRank as independent votes that boost Expedia’s credibility.)
Why does Google, if it’s interested in serving searchers with good information, reward a page like that? It has been suggested it is because if Expedia were missing from search results where people would expect to find it, people would doubt whether Google search was working correctly.
So, small businesses are being made to adhere to standards that big businesses can ignore.
If, according to Google, nobody much would notice if your business is missing from the results, and you violate Google’s Quality Guidelines, Google can algorithmically exact a penalty on your site. These penalties (with over 200 criteria) are not so easy to clear up. On the bright side in this vein, one of the best things you can do for your business in Google search, and your business in the world, is to build it, or to use the buzz-word, build its “brand” – so that it cannot be ignored. Then it will slough off Google Guidelines like it was launched by Bill Gates.
What exactly is a “Brand”?
I just saw a memorable branding of the bad guys by a red-hot metal bat-symbol in the Batman vs Superman movie. The word comes to business from livestock hide-marking. And it’s because of this connection that business-people understandably focus on the logo; David Ogilvy taught advertising agencies in the 1980s, an already decades-old chant: “If your client groans and sighs, make his logo twice the size.” Ogilvy was grumpy about it, because a symbol is really an almost inconsequential part of doing business. And, as concerns our topic, symbols are unreadable, and so, useless, to Google search, demonstrating that there is much more to the idea of “brand” to get a good Google rank.
It’s hard to argue against market-dominance being a factor in having a business that is acknowledged with a top position by Google. But there are great brands that exist in every industry, that win the rankings and sales appropriate to their business size and model. Bear this in mind when thinking about building your brand: establish its role in the market (or sometimes alternatively called, “mission,” or sometimes “vision”) and values (what are the means by which the business will fulfill its role).
The more consistently these ideas are both articulated verbally and non-verbally, and most important, repeatedly put into practice, the meaning of the brand will be revealed. And how will it be revealed? Ever heard the expression, a business has the customers it deserves? Well the meaning of your brand will end up being reflected back to the business in the form of recognition. And recognition can take many forms:
- Conversations on social media,
- Reviews on Facebook pages and other websites,
- Awards from trade associations, links from industry peers,
- Citations in industry publications, and so on.
(It’s also not a bad idea to get the ball rolling by asking industry colleagues and customers on occasion to discuss via social media a page you’ve added to your site.) The main benefit of all this is that your organization gains in reputation and therefore credibility (and along this path, a good Google rank), and therefore sales or for a nonprofit, another form of fulfillment of its role.
They Call Me the Seeker
Most of the web has been built ignoring data about how people search. And that’s as it should be. For instance, if you have a specific story to tell, if you are building a page or site for a specific community that is being directed to the site in other ways (this newsletter, for example, is created to help the Bryley community), or if you have research to publish.
But if you want your site to be found by strangers among the billions of web pages, consider how people are using the web, which leads back to the idea of getting a good ranking by thinking like a searcher. Start by asking yourself:
- In my field what are the questions that Internet searchers are asking?
- What is the motivation behind the searchers’ questions:
- Are they looking for free advice only?
- Are they looking to see who is an expert that they can hire?
- Are they looking to connect with people with similar interests?
- How are the searchers asking those questions:
- What are the popular resources for those kinds of queries?
- Why do you think those sites are popular?
- What words are people using to search?
If you’re not, get familiar with Google AdWords’ Keyword Planner; for the last couple of years you’ve needed to sign up for an AdWords account to access it and it is designed for Google’s paid search-results program, but the data is derived from Google searches, and so helpful in understanding what’s being searched for.
One of the best ways to use the Keyword Planner is to enter a top-Google-ranking competitors’ site in the field revealed after you select Search for new keywords using a phrase, website or category. Google usually does a great job in parsing the site, giving few irrelevant returns, but it gives a lot of returns. But these can be filtered in the menu to the left, entering, for example 1000 searches/month and a minimum bid of $1.50, as recommended by Dan Shure in the AdvancedWebRanking blog. This will minimize the keywords that no one searches for and reveal those few that businesses value.
Once you have a keyword or keyword phrase about which you’re planning to build your page, now what? How do you avoid having a page like Expedia’s keyword-stuffing example that violates Google’s Quality Guidelines, yet still able to attract the interest of Google?
Short answer: put the keyword or keyword phrase in the title tag of your page. Also include it in the “keyword:description” meta-tag. This meta-tag is what Google will likely use as the search-return description under the link to your page. This meta-tag is not there to be seen by Google, but by a prospective visitor, so the description should contain the keyword or a supporting idea, be plain-English and be compelling to invite a click – after all it is these people that we’re really interested in, not Google.
Long answer: as Bill Gates said years ago, “Content is king.” And thanks to
Google’s synonym-support, the content of the page should not be redundant, but reflect the variety of terminology used to explain a given subject. And understand that authoritative content, as Google prefers, means at least 500 words on your subject per page. Matt Cutts, head of Google’s Webspam team advised, “For example, if you’re talking about a USB drive, some people might call it a flash drive or a thumb drive”.
Bear in mind the terms that people will type and think about synonyms that can fit naturally into your content. Don’t stuff an article with keywords or make it awkward; rather, incorporate different ways of talking about a subject in a natural way.
In May 2015, Google announced that the share of search on mobile outstripped search on PCs for the first time. With the announcement came suggestions for organizations to make their sites able to deliver information in the moment it is wanted, meaning make sure your site’s load time is speedy. To test and improve this factor in Google rankings, Google created the PageSpeed Tools. (To test your page-download speed, enter a web address in the field and click “Analyze”.) The PageSpeed Score ranges from 0 to 100 points: A higher score is better and a score of 85 or above indicates that the page is performing well.
While not a wholly comprehensive accounting of what it takes to be in the first rank of a Google search, the suggestions covered here are consistently the biggest effecters: being the kind of organization that makes people link to its content, creating content that answers what searchers are seeking, and making sure your pages load fast.
Funnily enough, these answers are not too different than thinking about getting your page ranked twenty years ago when Dave and Jerry at Yahoo! were linking to pages manually. But unlike then, no one sees the same results.
Search history is recorded and weighted in the results (unless a searcher opts out), and social connections are recorded and weighted in the results (unless a searcher opts out). Couple these with a physical location to get the results shown by Google and Bing.
For the web developer, strategically not much has changed, except the weight is maybe more strongly on reputation. But if you’re developing a site, how do you see the results without being affected by these filters and get a truer sense how your site is faring? You’ll have to choose these settings in your browser: Chrome, Incognito Window, Firefox, Safari and Internet Explorer, Private Browsing.
1 Google notes to support these statements:
$500B market capitalization.
 Some of you may know, but Bryley has outgrown our current location in Hudson and will be moving to Clinton. Our new building is a historic 1937 post office that was completely renovated and modernized in 2004. It has more than 10,000 square feet, the majority of which we will occupy, and comes with glass-walled offices, broad sweeping staircases, an elevator, two kitchens, and more.
Some of you may know, but Bryley has outgrown our current location in Hudson and will be moving to Clinton. Our new building is a historic 1937 post office that was completely renovated and modernized in 2004. It has more than 10,000 square feet, the majority of which we will occupy, and comes with glass-walled offices, broad sweeping staircases, an elevator, two kitchens, and more.
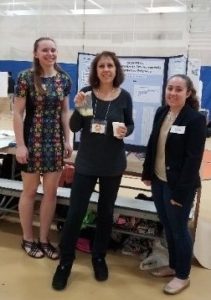
 Bryley’s Prestigious Channel Partners 360° Award also traveled to the event!
Bryley’s Prestigious Channel Partners 360° Award also traveled to the event! Bryley’s own Jessica Giunta (right), and Audrey Baker
Bryley’s own Jessica Giunta (right), and Audrey Baker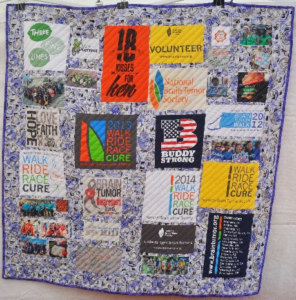 Jessica made the quilt that was on display during the event.
Jessica made the quilt that was on display during the event.
 The
The  workforce-development programs, and local small businesses.
workforce-development programs, and local small businesses.