Don’t Let the Summer Heat Destroy Your Mobile Devices
As much as we all enjoy outdoor activities that go along with those “lazy days of summer”, we are always reminded to stay hydrated, use sunscreen, avoid too much physical activity during peak hours, etc. But, what about our precious mobile devices? Are they being protected from the heat?
Here are a few things to remember as you’re out and about enjoying the warmth of the summer days. If you get hot, your mobile devices probably will too. Read on for a few helpful tips to keep your smartphones and tablets cool and running smoothly all summer long:
1 – If at all possible, charge the battery in your phone or tablet indoors where it’s cool. Charging any battery will cause it to heat up, and if the temperature is 90 degrees or above it could possibly cause the entire device to over-heat and fail.
2 – Try not to use your device in direct sunlight for extended periods of time on hot summer days, especially if it has a black or dark colored case. The sun’s hot rays can rapidly turn most any electronic device into a chunk of molten plastic and silicon, and typically, the damage is done before you even realize that it is happening.
3 – Install a quality anti-malware app on your devices to prevent viruses and malicious apps from over-working their CPUs and other components.
4 – Don’t leave your devices in a hot vehicle all day, even if the vehicle is in the shade when you park it. If you have no choice and simply must leave your device(s) in a hot vehicle, wrap it in a cloth and leave it in the trunk. Avoid leaving it in the passenger compartment.
5 – Use an app such as Clean Master or CCleaner for Android to keep your devices running as efficiently and cool as possible.These apps can help keep your device’s virtual working environment free of clutter, which in turn will allow the CPU and memory to work less while the device is running.
While we cannot control the outside temperature on a hot summer day, these steps can help protect your smart phones and tablets. Stay Cool!

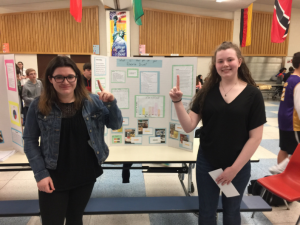 Winners of the 2018 Science Fair, Samantha Forde and Madison McDonald. Their winning display and science topic was “What is the PH of your Favorite Drink?”
Winners of the 2018 Science Fair, Samantha Forde and Madison McDonald. Their winning display and science topic was “What is the PH of your Favorite Drink?”