Here are six attendant mistakes that come from disregarding the six items at the foundation of Bryley’s Business Continuity Pyramid.
Heard of the Top Ten? The Final Four?
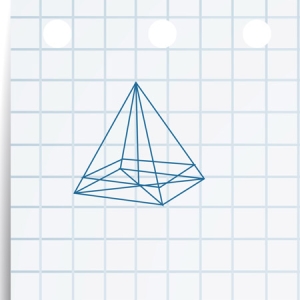
The Business Continuity Pyramid was built to be generally instructive about what Bryley has discovered to be foundational to an organization’s cybersecurity. The foundation of the pyramid shows these six cybersecurity recommendations:
- Comprehensive Support Program (CSP) Basic
- Security Updates
- Email Protection
- Anti-Virus/Anti-Malware
- AI-Enabled XDR (Extended Detection and Response)
- Assessments
These six were chosen because these items do the essential work that keeps an organization going despite the many threats every business faces.
So that begged the question, what if these six items were ignored? What might be the impact? Every organization is unique, so, the following is not exhaustive, but a general summary to invite consideration.
Bottom Six Mistakes Businesses Make with Cybersecurity
Not Patching Vulnerable Software
The number of weekly reported vulnerabilities is staggering (29,000 were reported in 2023). All these vulnerabilities need to be evaluated with regard to the system your organization is running. To organize and prioritize the patching you need to know which of these vulnerabilities, if they were to be exploited by a criminal, represents the most risk to your operation. And importantly, which of these corrective patches will not interrupt your employees’ workflow if you decide to install them? These considerations must be addressed before a patch is installed. Failing to address a patch is one of the key culprits behind many of the most notorious, as well as many of the less-proclaimed small business, breaches1.
Improper Handling of Email Attacks
From the common emailed phish that tries to get someone to click a link to deliver malware or trick the recipient into divulging their credentials to more targeted and expensive Business Email Compromise (BEC) attacks, businesses get inundated with email criminal activity.
One problem is that many organizations don’t articulate what employees should do if they encounter a phishing or BEC attempt. And sometimes the message to not click can cause someone who has clicked to fear reprisals if their mistake is found out. Itpro.com reported forty percent of people who clicked bad links got fired 2. Is this fair? Have pressures within the organization led to someone having a momentary lapse of judgment? The right message arriving at the right time and … even system administrators have clicked their own phishing simulations by mistake.
But the repercussions for the business of someone clicking a link and not reporting can be severe – for instance getting malware in the network. For BEC, the financial losses may be high, but failure to report BEC, though it may hide immediate shame, can lead to costlier lawsuits if, for example, payments are sent to a criminal and not a vendor.
So email scams need to be dealt with using a more helpful strategy that includes better containment of dangerous emails, employee training and organizational policies that encourage people to report that they have been tricked so real damage can be contained. Keep in mind that in a recent study over 10% of simulated phishing attacks were clicked and more than half of the people who clicked gave up credentials3. Phishing is about the oldest email trick in the book and it’s still in use for a reason.
Having a False Sense of Security
Without assessments of your as-is state, adding cybersecurity solutions may feel like the right idea, but every organization is different. Each has its own variables: How many remote workers are there? Do they bring their own devices? Do they use home networks? Does an organization run legacy software? Does it own legacy equipment? Does it rely on connected Internet-of-Things (IoT) devices? Skipping an assessment may mean leaving gaps in your protection. And you won’t know until one of these gaps is the entry-point of an attack.
Wanting IT Support After the Fact
Desperate business managers call Bryley after having lost important files or because they’ve been shut down and they had no reliable back-up and no remediation strategy in place. With a contracted managed service provider like Bryley, they probably would have had a plan in place. Now they are hoping that someone can undo an attack or equipment failure. They also in the moment want to undo their lack of preparedness. We feel bad and there are drive remediation services that can sometimes help, but having an IT resource to advise your technology decisions can help your organization stave off such desperate times.
Unleashing Ransomware
Ransomware is a branch of malware that locks a computer system so that files are encrypted and cannot be accessed while presenting a message with payment instructions so you can receive a decryption key.
If configured properly anti-virus and anti-malware software is regularly updated to identify computer virus and malware characteristics, including for ransomware. These tools scan a network for instances that match the virus/malware’s code. If the software finds an offending file in a downloads folder, for instance, it will issue a notification and quarantine the dangerous file so it can’t do harm.
Anti-virus and anti-malware are often cost-effective ways of behind-the-scenes blocking known viruses/malware.
Not Capable of Meeting Evolving Threats
Threats have evolved to include:
- The Exploitation of IoT Devices’ Vulnerabilities
- Fileless Malware
- because it is not a file, it does not have a signature that can be found by anti-virus/malware
- Insecure Cloud Configurations and Exploiting Cloud Infrastructure
Large enterprises have adopted detection and automated analyses that through both Software-as-a-Service (SaaS) and more broadly-available AI have trickled down to SMBs (small- to medium-sized businesses) in the forms of EDR (endpoint detection and response) and XDR (extended detection and response). XDR provides an overview of devices on your network (not limited to the endpoints [typically networked PCs] of EDR). XDR logs activity on networked devices and through AI learns and builds a dataset of typical activity on your network. When there are deviations from normal activity it has the ability to isolate a segment of the network to contain any potential threat from moving further. Most often EDR/XDR will log incidents and notify security analysts to investigate an event that has deviated from your network’s norm. This approach can also raise false warnings, so you need good analysts to sort actual attacks from benign, but atypical uses of your systems.
Helps Keeps Organizations Running
The Business Continuity Pyramid was created to show what Bryley considers basic for network security (at the bottom) up to the truly proactive virtual Chief Information/Technology Officer (vCIO/vCTO) in which a computer systems team helps your executives formulate the way to achieve your business goals. To begin to find out if Bryley’s business continuity approach is right for your organization, consider a complimentary 15-minute consult with Roy Pacitto, or contact Roy at ITExperts@Bryley.com or 978.562.6077 x2.
1 https://www.verizon.com/business/resources/reports/dbir/2024/ shows exploited vulnerabilities growing 180% in 2023; representing about 17% of breaches.
2 https://www.bryley.com/402 (scroll down).
3 https://static.fortra.com/terranova-security/pdfs/report/fta-tn-gone-fishing-tournament-report-rp.pdf
Lawrence writes about networking and security. He’s written for Bryley since 2015.

