Up Times
Up Times · April 2025

Good to have physicists to advise, engineers to design, craftspeople to build to maneuver at high speeds.
The speed of doing business … Can it super-power our work? Must we embrace it to stay competitive? Can it help us scale? And it opens wide a can of cybersecurity worms (no pun intended).
So how about getting a team of knowledgeable advisors to help your organization strike the perfect balance between AI tools needed to get you where you want to go and your organization’s appetite for risk?
That is, to me, Bryley’s ultimate role – being the C-Suite advisor. In support of this, COO Anna Darlagiannis-Livingstone heads Bryley’s R&D team that encompasses people from multiple tech disciplines. The team experiments in sandboxed [or contained] environments so by the time tech reaches Bryley clients, not only are the solutions vetted, but they arrive with a team who already has valuable hands-on experience. This is how Bryley has responsibly rolled out AI-based solutions like criminal-behavior-detecting EDR and an AI tuned to protect instances of M365. No matter how small it may seem, Anna said, the consequences may be large if you don’t think [deployments] through.
So go for the tech gains you want without endangering more than you can stomach, by talking it through with Bryley’s Roy Pacitto at RPacitto@Bryley.com or at 978•562•6077 x 217.

When what’s important is at stake, should you make it easy for criminals?
Leaving the key under the doormat? SSO can fix that
Single Sign-On gives employees secure access with minimal hassle
At the very least the current AI-dominated climate has made attacks more relentless and deceptive.
That means the fundamentals of security need to be in order. If your employees have questionable password practices like easy-to-guess passwords or passwords being reused or if they change their passwords just the bare minimum amount, or are using vulnerable SMS texts as the second security factor, you should consider Bryley’s Single Sign-On (SSO) offering that’s been showing high-adoption because it’s easy to use with a simple interface … [5 min. read] Continue Reading >

Swimming in data
Even increased efficiency can create new problems. With more efficiency comes the thought to collect more data.
–Data Analyst Brian Degon
AI goes fast. And because of this it amplifies the challenges to data security. For one example I saw on the way to posting this interview: in a joint Boston-area-school study of OpenClaw – an autonomous agent intended to take over a machine and work on behalf of the machine’s owner – the variety of security troubles the agent got in surprised even the researchers who were anticipating some problems.
And this brings us to the fundamentals, that brings us to my talk with Masters Academy International (Stow, Mass) data analyst and Bryant University adjunct professor Brian Degon. Previously Brian spent twenty-three years as a data and process analyst for WPI in Worcester, Mass … [5 min. read] Continue Reading >
According to SANS instructors, Anthropic’s claims about Mythos are both PR and a harbinger of the scaling of attacks that LLMs provide.
On the Mythos press release
Anthropic’s Mythos is more wake-up than departure
SANS (SysAdmin, Audit, Network, Security) Institute looked at the cybersecurity claims about Mythos. Those claims include uncovering some serious zero-day (aka as-yet-unknown) vulnerabilities.
Pen-tester Chris Elgee explains how LLMs (Large Language Models) are being incorporated into the hunt for vulnerabilities, models are really good at … for example … if you need to build out a proof-of-concept (we’ll take a slice of the code that we’re going to be looking at and just rebuild that as a local application [that] we can test against [e.g. safely sandboxing to show the vulnerability]) … Another thing they’re great at is searching for patterns [like for] filtering input a certain way … [asking the LLM] ‘where else can we find this pattern?’ … Also … code can be a mess. We’re going to look here at a code platform that’s about half a gig of code and well over a million lines of code and humans can follow those code trails but it takes us a long time … LLMs are good at following that … Lastly, iterating [testing repeatedly changing one variable at a time]. We humans get bored. We get sick of looking back at that same block of code again. We don’t want to test it one more time but the LLM doesn’t mind. It’ll iterate through as many times as you want.
Bottom line is that LLMs compress time.
One of the important take-aways is that in the race between criminals and the defenders that are patching systems, the advantage is always going to be asymmetric: advantage criminals. If LLM tools find vulnerabilities at a rate that far outstrips humans, how will we know which of the many exposed vulnerabilities to focus on and patch?
So although yes, we’re going to be seeing a lot more exploits, Senior Security Analyst Josh Wright says, the traditional controls also help us significantly. Limit the blast radius. When a system gets compromised, what else can the attacker do? [So] reduce your excess access. Privilege management and [Identity Management] systems need to be carefully scrutinized … limit what an attacker can do and what privileges somebody has access to … [1 hr watch] youtube.com
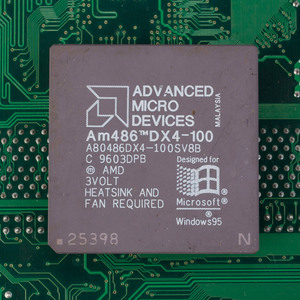
The speedy-for-the-time 486DX4 100 MHz CPU
Windows 95 is thirty
The Graphical User Interface version that separated Microsoft’s offering from the pack
Windows 95 established many of the familiar desktop OS’ lasting features like solidifying the desktop with its files and folders interface, long file names, right-clicked context-appropriate menus, 32-bit drivers that prevented many resource constraints and acting quicker by running as a true OS, not a skin on MS-DOS.
Here’s a graphical user history of Windows … [8 min. read] pcmag.com
Running on fumes?
No such thing as bad publicity
Among other things, Anthropic has been down. As in outages.
Usage at LLMs (Large Language Models) is increasing (12.8% year over year, per McKinsey). Can the building of data centers, the supply of GPUs and RAM, the electrical grid, the bandwidth support this continued growth?
And moreso, are you considering building a process around an LLM? What would happen if that LLM became inaccessible? Like any other resource, you’ll need to anticipate and plan – as in redundant LLMs – in order to maintain uptime. And just like any LLM you’ve adopted, the backup LLM shouldn’t leak its collected data … [7 min. read] techradar.com

c’mon man
The less data, the less risk
About the size of it
The GPC (Global Privacy Control) is a W3C (World Wide Web Consortium) initiative to standardize a signal sent via a web browser to a web page whether its user wants to opt-out of tracking.
It’s not so much that Google, Microsoft’s Bing and Meta, in this study, didn’t honor this opt-out privacy signal, they are actually shown to have coded responses that … well: when Google’s server responds to the network request with the opt-out it explicitly responds with a command to create an advertising cookie. On Microsoft’s Bing.com: Microsoft’s server responds by setting … a one-year advertising tracker. And on Meta: loads unconditionally, fires a tracking event, and sets a cookie regardless of the consumer’s privacy preferences.
So if you use these services, try and opt-out from tracking one by one: myaccount.google.com/privacycheckup, account.microsoft.com/privacy/, facebook.com/privacy/center/. And each of these claim to honor optout.aboutads.info – so it’s worth a shot (though they – is their heart in it? – don’t make it easy)! … [10 min. read] globalprivacyaudit.org

Some kind of party
Twenty years since the iPod to iPhone revolution changed how we live
The father of the iPod looks back at how Apple redefined its business
Tony Fadell was interviewed by CNN ostensibly about the iPhone, but the iPod contained many of the seeds of what would become the iPhone’s trajectory. It was Fadell that began the iPod’s annual re-creation that has been adopted in the iPhone’s annual events – and so Apple continues to ship a lot of units every year. The story is instructive to anyone insisting that their product is right before its launch.
Not contained in the article are Fadell’s previously expressed discomfort about having helped birth the ubiquity of screens at the expense of human-to-human interaction. And his 2017 points are solid, but don’t touch on the business costs – for instance with the rise of Zoom calls, deepfakes, faceless marketplaces and similar, we lose many of the tells that let us know what’s a rip-off – like fidgety nervousness or facial signals that something’s not right about a transaction … [7 min. read] cnn.com
Note: The section directly above is Bryley’s curated list of external stories. Bryley does not take credit for the content of these stories, nor does it endorse or imply an affiliation with the authors or publications in which they appear.
Get Up Times, useful tech news by New Englanders in Your In-Box
- Subscribe to Up Times, the monthly New England-centric technology newsletter.
- Up Times covers:
-
- Trends in New England tech
- Security tips you can implement now
- Updates on regional and national laws and compliancies
- IT-related developments
- Networking and cybersecurity challenges New England business managers are facing
- In continuous publication since 2000, Up Times arrives monthly in your email box.
Sign up for Up Times to have tech news and tips delivered monthly via email

Services

