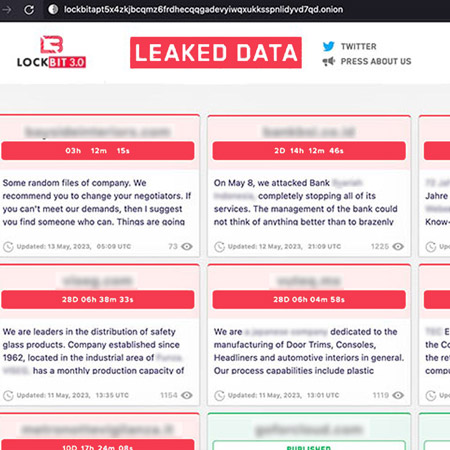
A redacted portion of a dark web page from criminal group Lockbit. The victim organizations in pink squares have countdown timers until their data is released on the web; the green squares, lower right, show the organizations whose data has already been publicly leaked.
Source: bloombergtechnoz.com
Evolution of Evil
Ransomware is a somewhat straightforward criminal action – data is illicitly encrypted and you may be able to restore systems from a backup or pay the crooks to hopefully get a decryption key from them.
Things have veered in a different direction now (see Allianz Commercial insurer’s report). Today a lot of ransomware attacks are cyber-extortion attacks. In these attacks the criminals capture your data and encrypt it, but they also exfiltrate your data to their servers. And the threat is often, ‘unless you pay, we will release your data on the web,’ see the screenshot of Lockbit’s web page, at right.
And what if your data is leaked?
- Organizations can face fines, lawsuits and the remediation costs that are associated with losing and recovering data
- An organization’s reputation can take a hit as it has literally shown that client or other data is not sufficiently protected. This can result in lost customers, lower sales and difficulty hiring people
- Operation disruptions, which can lead to organizational downtime and lower productivity. The data theft and encryption may damage your infrastructure
Getting in
First, it’s important to understand how the ransomware ended up on your network. In most cases criminals depend on organizational negligence or employee error to get in. The most common ways, per the Center for Internet Security1, are via unsecured remote access or an employee clicking on a bad link.
Remote access should be achieved within a virtual private network (VPN) that in a protectional way creates an encrypted tunnel for your organization’s moving data. Also remote access should be secured using multi-factor authentication (MFA).
Regarding clicking on bad links Bryley advocates a layered approach. This includes quarantining suspicious emails and denying access to suspected websites. A password manager can also help for websites; employees may not see that a letter is missing in a spoofed domain name, but software is unlikely to be fooled by a similar, but different domain name2.
And consider keeping your employees up-to-date through regular training on the shifting tricks criminals use to get us to click on trouble.
How can least privilege help?
The principle of least privilege (PoLP) means your employees are provided with the bare minimum privileges. The bare minimum means only granting the ability to access a process, software program, device or other users in order for an employee to perform a function. For instance, if a user account has been created for accessing database records, the same user account does not need to be an admin. Also, a programmer responsible for updating lines of code can do so without being able to access the organization’s financial records. It’s a simple concept that if executed properly and consistently makes a real difference in the event of an incursion – it’s an important layer in a sound defense stack, as it:
-
- Lessens the Attack Surface
- Restricting privileges for your applications, processes and users cuts the overall attack surface and limits the points of ingress for criminals to exploit
- Reduces the Impact of Breaches
- If a user account that has only limited privileges is compromised, the scope of catastrophic harm may be low
- Slows Malware Infections
- A SQL code injection, one of the most common attacks, inserts malicious instructions into benign code. These instructions allow the hacker to enhance his privileges and acquire unauthorized control over your critical systems. PoLP can restrict the attacker’s ability to escalate privileges and access sensitive data. This can buy time for defenders to detect and respond to the attack.
- Lessens the Attack Surface
Thorough and thorough
PoLP needs to be applied consistently and comprehensively across all systems and applications. Incomplete or inconsistent implementation can leave holes for attackers to exploit. Bryley advocates the use of Microsoft’s Active Directory (AD) to govern the implementation of privileges. One of AD’s great strengths is that it permits the centralized creation of user- and group-based policies, permissions and privileges3; it can then enforce these so that members must comply with login and usage requirements. It also logs violations and login attempts to help in securing your network.
Granting least privilege to accomplish a task can help keep extortionware criminals at bay. Contact Bryley by the form, below, or at ITExperts@Bryley.com or 978.562.6077 x2 to learn if your organization would benefit from leveraging the powerful capabilities of PoLP.
1 https://www.cisecurity.org/insights/blog/ransomware-the-data-exfiltration-and-double-extortion-trends
2 Another common way criminals get into networks is through poor password behaviors, like password reuse. The recent 23andme hack has been blamed on reused passwords. Employing a password manager can cut down on poor password practices.
3 Policies can be thought of as the overall rule book. Privileges are like a master key. And permissions let that master key work in a specified way on a particular resource.

President, Bryley Systems. Since 1987 Mr Livingstone has steered Bryley to continuous growth with over 250 clients throughout New England and the US. He has extensive knowledge of technology and business operations.


